7 Security Design Patterns Every Azure Architect Must Know
Designing secure Azure solutions isn’t just about enabling Defender or turning on encryption. True security architecture is about consistent design patterns that reduce attack surface, isolate workloads, and enforce least privilege across the cloud estate. As Azure evolves, solution architects must understand these patterns deeply enough to apply them automatically when designing new workloads or reviewing existing environments.
Pattern 1: Zero Trust Network Segmentation
The modern Azure perimeter is identity-based, not network-based. Zero Trust requires verifying every request — user or service — before allowing access. Implement this by creating smaller, purpose-driven VNets and subnets, applying Network Security Groups (NSGs) for layer-4 control, and Azure Firewall for layer-7 inspection. Pair segmentation with Conditional Access and Defender for Cloud to ensure no implicit trust remains between workloads.
Pattern 2: Secure Identity and Access Control
Identity is the new security boundary. Azure Entra ID (formerly Azure AD) becomes the backbone for both human and service identities. Use Privileged Identity Management (PIM) for just-in-time admin elevation and Managed Identities for app-to-resource access. Assign permissions via RBAC at the lowest possible scope — never grant Contributor at subscription level unless required for automation pipelines.
Pattern 3: Protect Data at Every State
Data must be encrypted in transit, at rest, and in use. Use HTTPS/TLS 1.2+, enable encryption with customer-managed keys (CMK) in Azure Storage, SQL, and Cosmos DB, and leverage Always Encrypted for sensitive columns. For confidential workloads, explore confidential computing SKUs with hardware-based memory encryption.
Pattern 4: Private Connectivity to PaaS
Eliminate exposure of service endpoints to the public Internet. Replace them with Private Endpoints and Private DNS Zones. Restrict access to PaaS services like Storage, SQL, and Key Vault via virtual network integration. Combine this with an egress-controlled hub network so all traffic passes through a single inspection layer.
Pattern 5: Centralized Logging and Threat Detection
Visibility drives response. Consolidate logs from all subscriptions into a single Log Analytics workspace connected to Microsoft Sentinel. Stream activity logs, diagnostics, and Defender alerts. Use Analytics Rules for correlation and Workbooks for visualization. Every architecture diagram should show a log flow arrow — if it’s missing, it’s an audit finding waiting to happen.
Pattern 6: Secure Secrets and Configuration Management
Never embed credentials in code or configuration files. Store them in Azure Key Vault with RBAC or access policies and Managed Identities for retrieval. Use separate vaults per environment (Dev, QA, Prod) and enable soft delete and purge protection. Audit Key Vault access through diagnostic settings.
Pattern 7: Automated Compliance and Governance
Governance must scale faster than deployment. Use Azure Policy to enforce configuration baselines — encryption, tagging, diagnostic settings, SKU restrictions — and remediate drifts automatically. Group policies into Initiatives for larger standards (e.g., ISO 27001, CIS) and assign at Management Group scope. Feed compliance results into dashboards and integrate alerts into Microsoft Sentinel for proactive governance.
Common pitfalls
- Using NSGs alone without an Azure Firewall or WAF layer.
- Leaving diagnostic settings off for new resources.
- Granting broad access at subscription level instead of resource group level.
- Ignoring identity lifecycle — stale accounts and service principals remain open doors.
- No monitoring for failed login patterns or privilege escalations.
- Over-relying on defaults; many services deploy with public endpoints unless explicitly disabled.
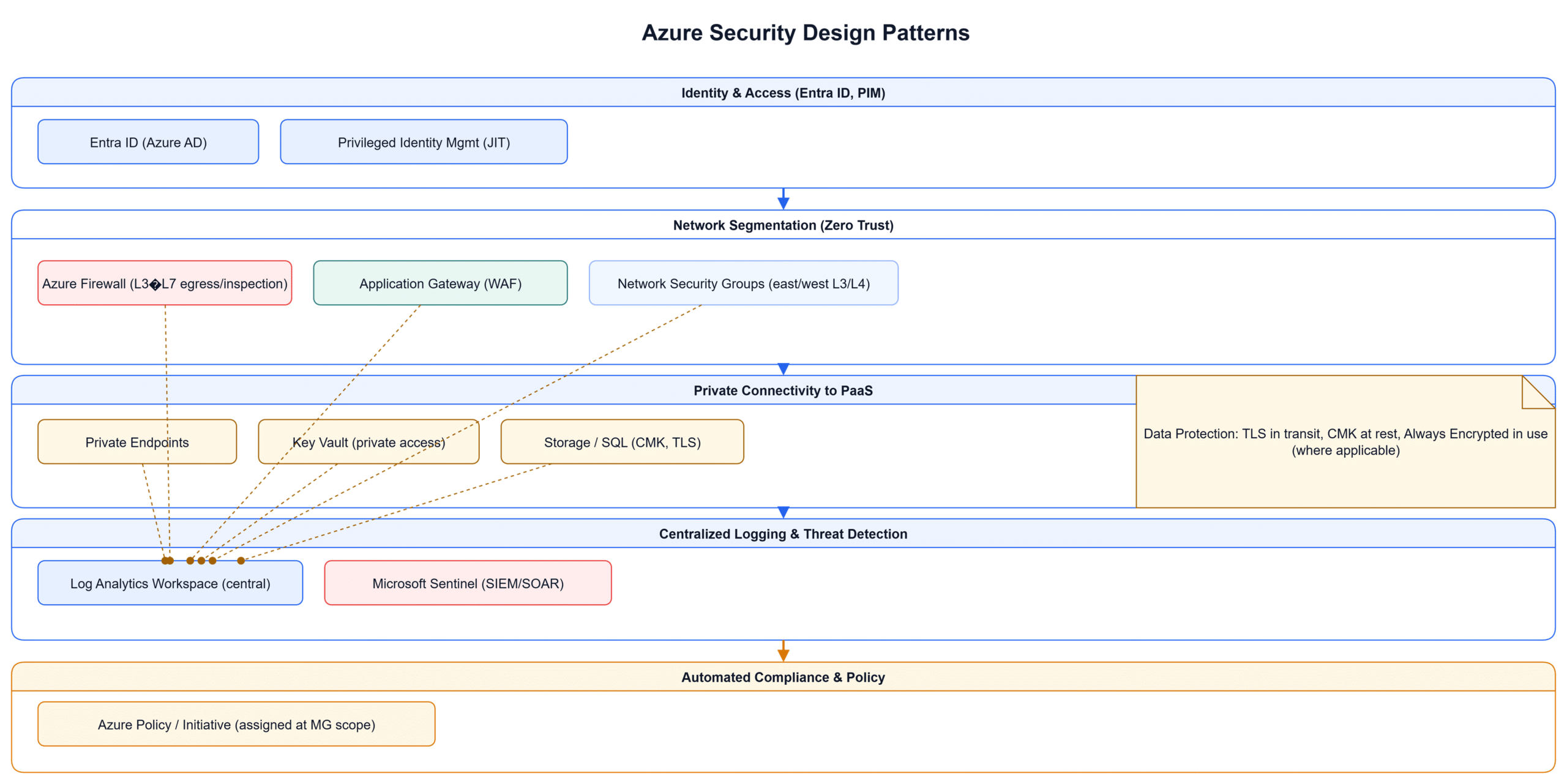
Diagram
The diagram illustrates a secure Azure environment applying all seven patterns together — from Zero Trust segmentation to centralized logging. It highlights identity integration, network isolation, private access, and governance flows that tie everything together.
Conclusion
Security is a pattern language — not a checklist. When architects internalize these seven patterns, security becomes a design habit rather than an afterthought. Combine them consistently and document trade-offs in your Architecture Decision Records (ADRs). This approach aligns with both Azure Well-Architected Framework and enterprise compliance demands, ensuring security by design at every layer.