Architecting for Security: How to Talk Like a CISO in Azure Interviews
In senior-level Azure interviews, security questions test more than your knowledge of encryption or firewalls. They assess how you balance protection, usability, and business agility — the same mindset a CISO brings to strategy discussions. To stand out, you must connect architectural choices with risk, compliance, and accountability.
1. Shift from “Controls” to “Risk Language”
CISOs speak in risk, not resource names. When asked about data protection, describe the risk reduced by using encryption at rest, private endpoints, or Azure Key Vault. For every control you mention, follow with “This mitigates …” to show business awareness.
2. Frame Answers Around the Shared-Responsibility Model
Azure’s security model divides duties between Microsoft (platform) and you (data, identity, and configuration). Interviewers want to see that you understand boundaries. Example: Microsoft secures the hypervisor; architects must configure NSGs, patch workloads, and manage access policies.
3. Use the CISO Triad – Confidentiality, Integrity, Availability
Map every architectural decision back to the CIA triad:
- Confidentiality: Use Entra ID, conditional access, and data classification.
- Integrity: Implement versioning, immutability, and Key Vault-backed signing.
- Availability: Design redundant regions, DDoS Protection, and health probes.
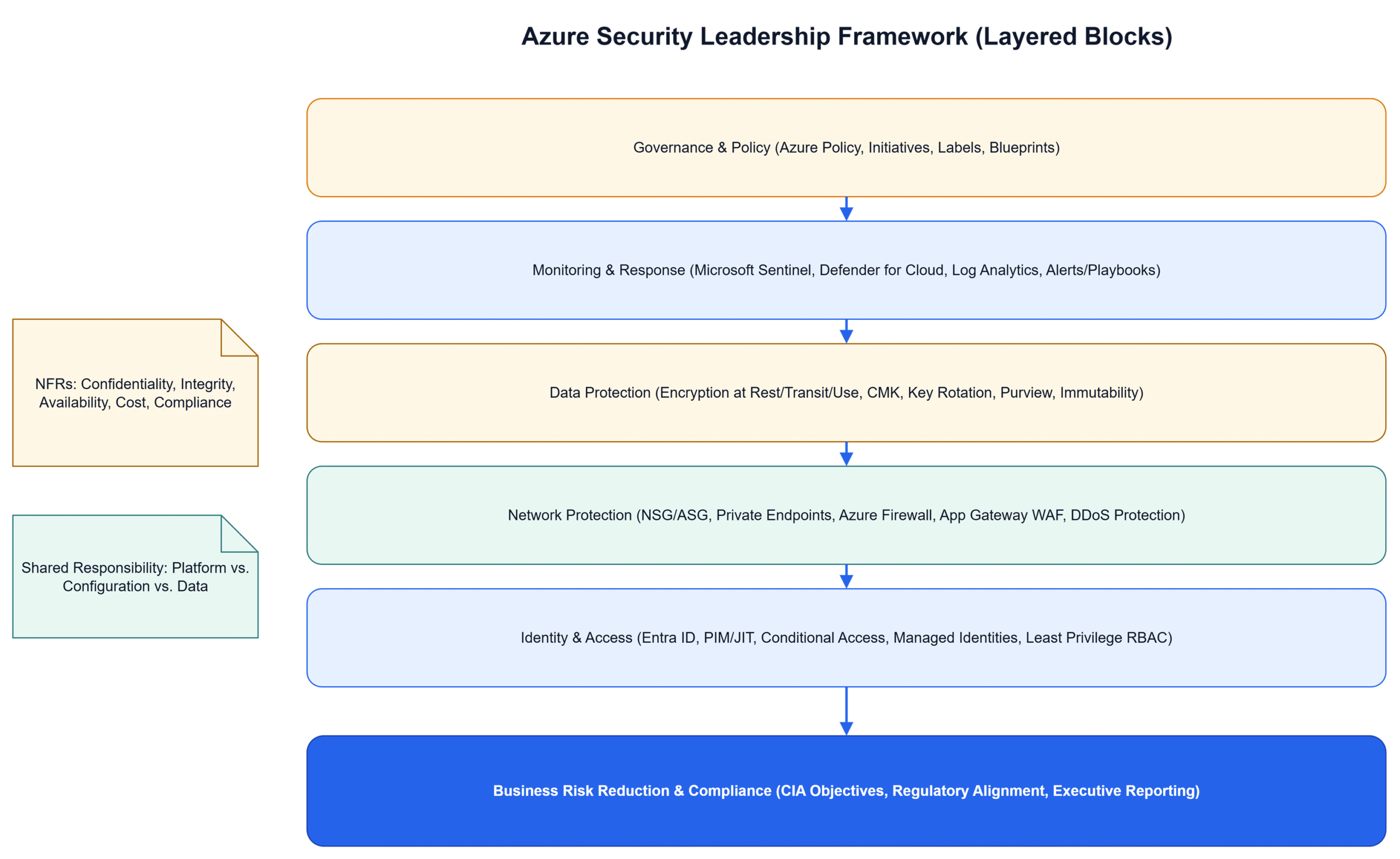
4. Demonstrate Layered Defense Thinking
Explain how each Azure layer contributes to defense-in-depth:
- Identity – Entra ID, PIM, Conditional Access.
- Network – NSGs, ASGs, Azure Firewall, Private Endpoints.
- Compute – Managed Identities, Disk Encryption, OS patching.
- Data – Transparent Encryption, Access Policies, Key Rotation.
- Monitoring – Sentinel, Defender for Cloud, Log Analytics.
5. Tie Security to Business Impact
When describing mitigations, mention the business consequence avoided. Example: “By enforcing private connectivity and CMK encryption, we prevent data exfiltration — protecting regulated customer data and avoiding GDPR penalties.” Framing answers this way shows executive maturity.
6. Common Mistakes
- Listing Azure services without explaining risk coverage.
- Focusing only on perimeter controls and ignoring identity.
- Not mentioning compliance frameworks (ISO 27001, NIST, GDPR).
- Failing to link security cost to business justification.
7. Use the “Secure-by-Design” Storyline
A powerful interview tactic is to describe how security decisions evolve with the architecture lifecycle:
- Start — Classify data and apply sensitivity labels.
- Design — Embed policy, identity, and network segmentation.
- Build — Use templates and DevSecOps gates.
- Operate — Monitor with Sentinel and automate responses.
This shows you understand continuous security, not one-time setup.
Diagram
The diagram illustrates how an architect can articulate Azure security to leadership — linking each defense layer to business risk reduction and compliance visibility.
Conclusion
Talking like a CISO means elevating technical security controls into a story about risk, governance, and trust. When you describe Azure solutions through that lens, interviewers see a strategist — not just a technologist. That’s the mindset of a true enterprise architect.