Azure Governance in Practice: Policies, Blueprints & Management Groups
As organizations scale in Azure, manual control over configurations and compliance becomes impossible. Governance is the architecture layer that ensures security, compliance, and consistency across subscriptions and teams. Microsoft provides three core building blocks for governance — Management Groups, Azure Policy, and Blueprints — which together form a hierarchy of control. This guide explains how they fit together, how to design governance at scale, and what patterns experienced Azure architects follow in production.
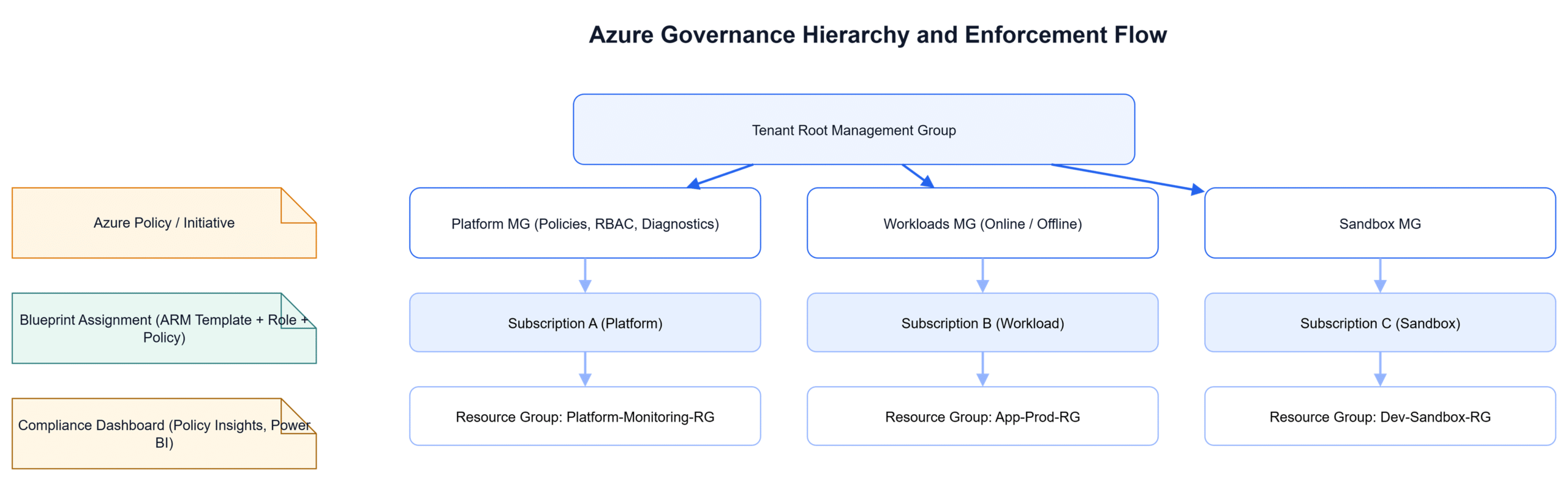
1. Understanding the Azure Governance Hierarchy
Governance in Azure is hierarchical and inheritance-based. Policies and permissions applied at a higher scope automatically cascade down. The structure follows a logical order: Tenant → Management Groups → Subscriptions → Resource Groups → Resources.
- Tenant root group: The top-level container for all assets and policy inheritance.
- Management Groups (MGs): Logical folders to group subscriptions by business unit, environment, or compliance type.
- Subscriptions: Billing and isolation boundaries where resource creation happens.
- Resource Groups: Contain deployable resources and inherit policies from higher levels.
2. Azure Policy: The Guardrails of Governance
Azure Policy enforces standards and detects configuration drift automatically. You can restrict VM SKUs, require encryption, force diagnostic settings, or enforce specific tags. Policies can be Audit, Deny, or DeployIfNotExists type, giving flexibility between monitoring and enforcement.
- Group related policies into Initiatives (e.g., ISO 27001, CIS Benchmarks).
- Assign initiatives at the Management Group level for enterprise consistency.
- Use Policy Exemptions carefully to handle exceptions with justification.
3. Management Groups: Organizing Control
Management Groups act like organizational folders. They enable structured application of policies, RBAC, and budgets at scale. A common hierarchy includes layers such as Platform, Online/Offline Workloads, Sandbox, and Decommissioned.
Design Management Groups to reflect business and compliance boundaries — not IT departments. Keep the number of levels minimal (usually 3–4), but meaningful for reporting and policy targeting.
4. Blueprints: Governance as Code
Blueprints combine ARM templates, role assignments, policies, and resource groups into a version-controlled package. They allow repeatable deployment of compliant environments — for example, a standard subscription baseline or a regulated workload environment.
- Store Blueprints in source control to maintain governance versioning.
- Assign Blueprints to subscriptions and lock resources to prevent drift.
- Use the new Azure Landing Zone Accelerator (replacement for legacy Blueprints) for modern deployments.
5. Governance at Scale: Automation & Monitoring
Use Azure Resource Graph and Policy Insights to query compliance across hundreds of subscriptions. Integrate governance compliance results into Power BI or Microsoft Sentinel dashboards. Automate policy assignment via Bicep, ARM templates, or Terraform pipelines. Treat governance as code, reviewed and deployed like application releases.
Common Pitfalls
- Assigning policies directly to subscriptions instead of Management Groups.
- Using too many overlapping initiatives leading to contradictory effects.
- Leaving exemptions unmonitored or without expiry.
- No ownership model for policy review and updates.
- Manual deployment of governance elements rather than CI/CD pipelines.
Diagram
The diagram below illustrates a standard Azure governance structure — showing Management Group hierarchy, cascading policies, and the integration of Blueprints for compliant deployments.
Conclusion
Governance is not an audit checkbox — it’s the backbone of sustainable cloud operations. By defining clear hierarchies, enforcing policies through code, and maintaining visibility through automation, Azure architects build confidence that every workload is compliant by default. The best designs make governance invisible yet ever-present — embedded in every resource deployment.